MIT engineers develop twin chip method to enable server-free fingerprint authentication
New CMOS fabrication approach allows paired chips to share a physical fingerprint, reducing reliance on third-party servers for cryptographic security.
Engineers at MIT have developed a chip fabrication method that enables two CMOS chips to share an identical physical “fingerprint,” allowing them to authenticate each other directly without storing secret data on external servers.
The approach could strengthen hardware-level cryptography while improving energy efficiency in constrained edge devices.
The technique, presented at the IEEE International Solid-States Circuits Conference, modifies standard chip manufacturing processes so that paired devices contain a shared physical unclonable function (PUF). By embedding authentication keys directly within the silicon, the method removes the need to register and store fingerprint data on third-party systems, a common vulnerability in existing cryptographic schemes.
Eliminating external key storage
Every CMOS chip contains tiny, unavoidable manufacturing variations that create a unique identifier, known as a physical unclonable function. These PUFs are often used in authentication systems, where a server verifies a device by checking a secret key derived from its physical structure.
However, traditional PUF-based systems require fingerprint data to be stored on external servers for later verification. That creates additional attack surfaces and increases memory and computational demands.
“The biggest advantage of this security method is that we don’t need to store any information. All the secrets will always remain safe inside the silicon. This can give a higher level of security. As long as you have this digital key, you can always unlock the door,” says Eunseok Lee, an electrical engineering and computer science graduate student and lead author of the paper.
To address this, the MIT team designed a method to create a matched PUF pair during fabrication. Two chips are processed together so that each contains a shared, identical fingerprint that is unique to that pair.
Creating shared randomness inside the foundry
The researchers achieved this by modifying transistor behavior at the edge of chips before they are separated from a silicon wafer. Using a process called gate oxide breakdown, they apply high voltage to transistor pairs using a low-cost LED until breakdown occurs. Because of microscopic variations, each breakdown event produces a unique pattern.
By linking paired transistors across adjacent chips before dicing, the team created correlated breakdown states that form a shared PUF. Once the chips are separated, each retains one half of the matched structure, allowing direct authentication between the two devices.
“We needed to find a way to do this before the chip leaves the foundry, for added security. Once the fabricated chip enters the supply chain, we won’t know what might happen to it,” Lee says.
After refining the process, the team produced a prototype twin PUF chip pair that demonstrated more than 98 percent reliability in matching keys, ensuring consistent authentication.
The approach relies on standard CMOS-compatible processes and does not require specialized materials, which could support scalability.
“Creation of shared encryption keys in trusted semiconductor foundries could help break the tradeoffs between being more secure and more convenient to use for protection of data transmission,” says Ruonan Han, professor of electrical engineering and computer science and co-senior author. “This work, which is digital-based, is still a preliminary trial in this direction; we are exploring how more complex, analog-based secrecy can be duplicated — and only duplicated once.”
Potential for low-power edge devices
The researchers suggest the technique may be particularly useful in non-interchangeable device pairs operating under energy constraints, such as ingestible sensor pills and wearable patches used in medical monitoring. In such systems, direct chip-to-chip authentication could reduce protocol overhead and eliminate intermediary servers.
“There is a rapidly increasing demand for physical-layer security for edge devices, such as between medical sensors and devices on a body, which often operate under strict energy constraints. A twin-paired PUF approach enables secure communication between nodes without the burden of heavy protocol overhead, thereby delivering both energy efficiency and strong security. This initial demonstration paves the way for innovative advancements in secure hardware design,” says Anantha Chandrakasan, MIT provost and co-senior author.
Future iterations may preserve shared randomness directly within transistor structures rather than converting it immediately into digital form, further embedding security at the physical layer.
While the work remains an early demonstration, it signals ongoing efforts to strengthen hardware-level cryptography at a time when AI-enabled edge devices, connected medical systems, and distributed computing architectures are increasing demand for low-power, high-trust authentication methods.
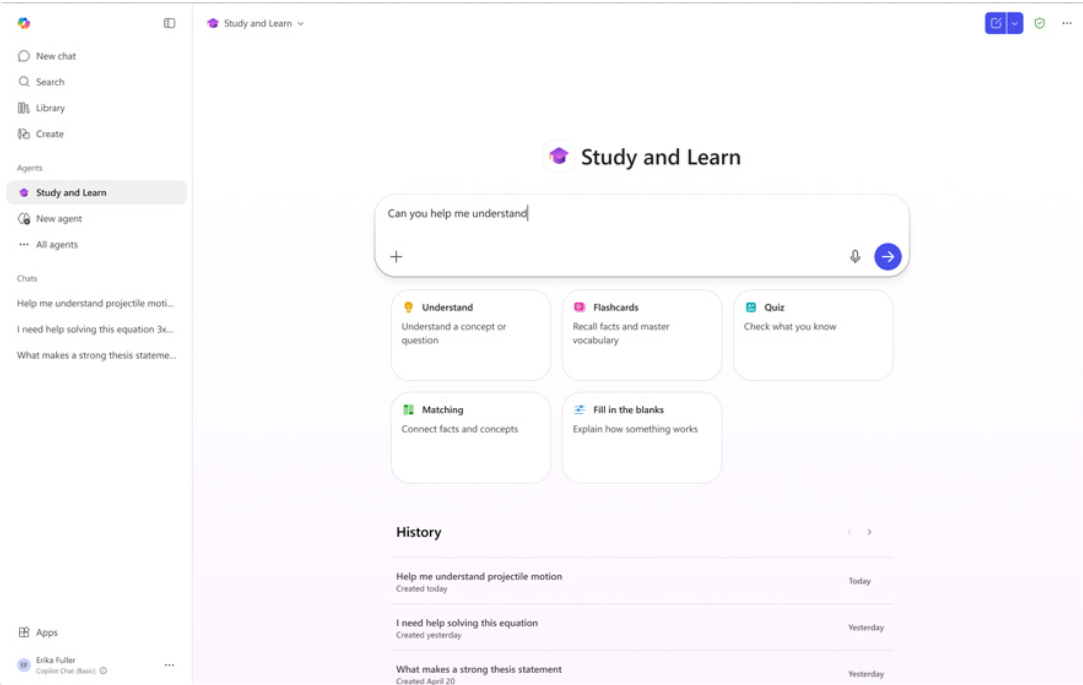
ETIH Innovation Awards 2026
The ETIH Innovation Awards 2026 are now open and recognize education technology organizations delivering measurable impact across K–12, higher education, and lifelong learning. The awards are open to entries from the UK, the Americas, and internationally, with submissions assessed on evidence of outcomes and real-world application.